TL;DR: You cannot migrate to post-quantum cryptography without knowing what cryptographic assets you have. A Cryptography Bill of Materials (CBOM) gives you a structured, standardized inventory — and open-source tooling now exists to build one automatically.
In our earlier post on post-quantum readiness as a strategic imperative, we discussed the steps organizations need to take for a successful migration to Post-Quantum Cryptography (PQC). Specifically, in this post we focus on one of the key prerequisites: building a comprehensive inventory of cryptographic assets.
Why Inventory of Cryptographic Assets Matters
Building an inventory of cryptographic assets is a fundamental first step in the migration to quantum-safe systems. Specifically, cryptographic assets are often deeply embedded within systems, applications, and infrastructure. Without a clear understanding of these assets, assessing risk and planning mitigation is impossible.
Moreover, in today’s dynamic environments, businesses must stay ahead by thoroughly discovering and managing cryptographic assets. Both efforts are critical as quantum computing poses growing risks to classical encryption.
What Should an Inventory Contain?
A thorough cryptographic asset inventory needs to include:
- Cryptographic keys. The building blocks of encryption. For each key, document storage type, ownership, algorithm, format, and status.
- Certificates. Electronic identities tied to public keys. Capture validity period, ownership, and algorithm.
- Algorithms. Track which algorithms are in use for encryption, authentication, and signing. Flag those vulnerable to quantum attacks.
- Protocols. TLS, IPSec, and similar protocols that define cryptographic operations. Document version and implementation details.
The Process of Building an Inventory
Step 1: Discovery and Identification
The first step involves identifying where cryptographic assets are used across your infrastructure. These assets could be stored in:
- Certification Authorities (CAs)
- Servers and databases
- Hardware Security Modules (HSMs)
- Network traffic, including encrypted traffic
- Cloud providers
- Containers and microservices
However, given the complexity of modern IT environments, relying on spreadsheets is impractical. Instead, automated tools that support discovery across diverse platforms are essential.
Step 2: Collecting Asset Properties
Once discovered, you need to gather metadata about these cryptographic assets. This includes:
- Ownership — who is responsible for managing the cryptographic asset?
- Application — what applications or systems are using the asset?
- Dependencies — what other systems, libraries, or services depend on the asset?
Together, these details give organizations the context to manage risks effectively — particularly as they transition to post-quantum cryptography.
Step 3: Building a Robust Inventory
A well-structured inventory provides several benefits:
- Planning. Identify outdated algorithms and assets that need replacement or upgrade.
- Risk assessment. Regular monitoring allows proactive risk management. Track compliance and progress toward quantum readiness.
- Identifying dependencies. Knowing how assets are interconnected prevents outages during migration.
Leveraging the Cryptography Bill of Materials (CBOM)
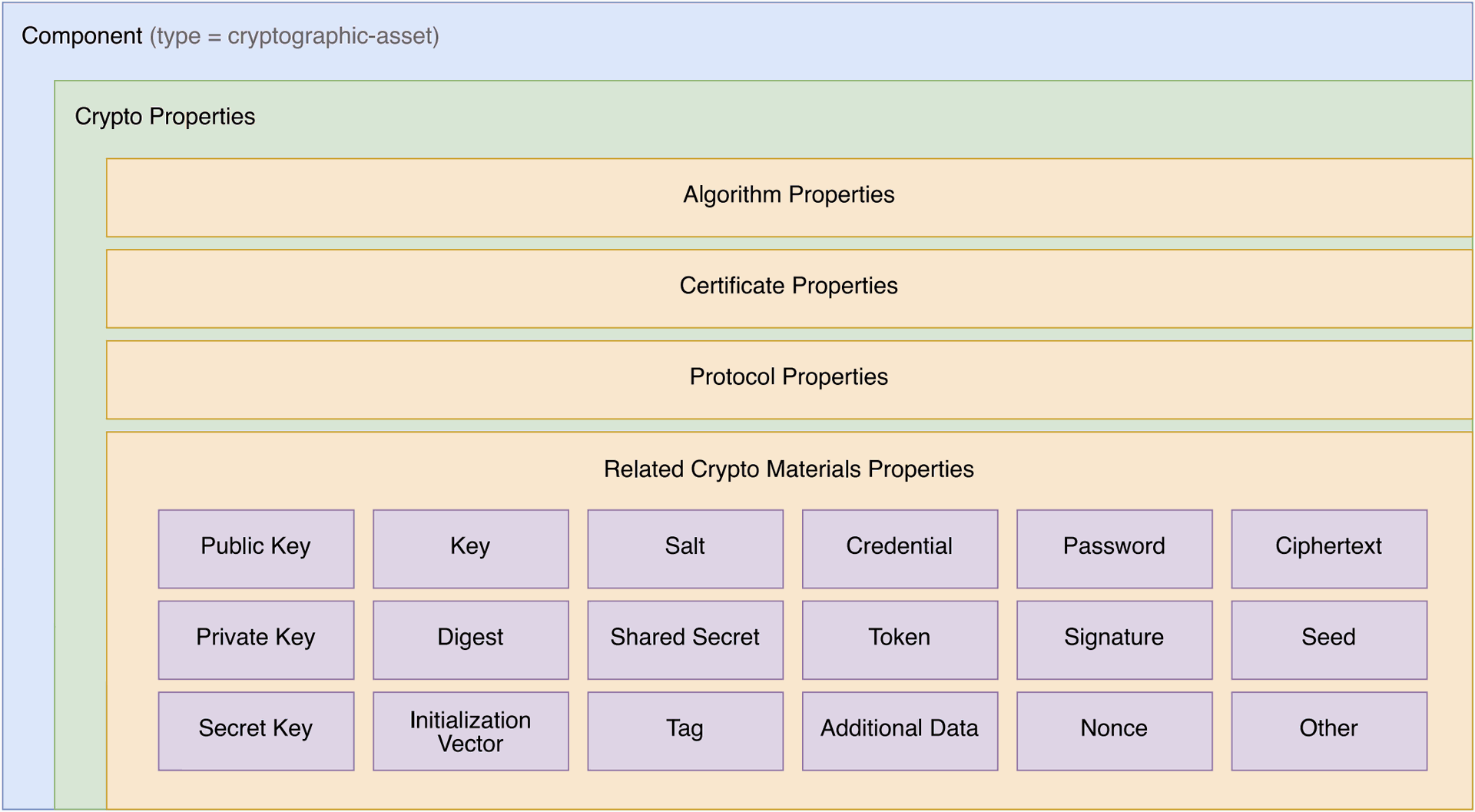
To streamline and standardize the inventory process, many organizations are turning to the Cryptography Bill of Materials (CBOM). The CBOM is an extensible model that allows organizations to describe cryptographic assets and their dependencies in a structured format. Importantly, it is part of the OWASP CycloneDX framework, designed to reduce cyber risks by providing a detailed picture of cryptographic infrastructure.
Key Features of CBOM
- Modeling cryptographic assets — CBOM provides a framework to model keys, certificates, algorithms, and protocols.
- Capturing asset properties — it captures key attributes such as algorithm type, key length, usage details, and more.
- Tracking dependencies — CBOM maps out dependencies between different cryptographic assets and the systems that use them.
- Compatibility with CycloneDX. CBOM integrates with the CycloneDX SBOM standard, making it easy to add to existing supply chain tools.
The diagram below shows the structure of a CBOM component. Each cryptographic asset is described through its crypto properties — algorithm, certificate, and protocol details — along with related crypto materials such as keys, secrets, tokens, and signatures.
Example: Cryptographic Key in CBOM
Here is how a cryptographic key might be represented using CBOM in the CycloneDX format:
{
"components": [
{
"name": "RSA-2048",
"type": "cryptographic-asset",
"bom-ref": "crypto/key/rsa-2048@1.2.840.113549.1.1.1",
"cryptoProperties": {
"assetType": "related-crypto-material",
"relatedCryptoMaterialProperties": {
"type": "public-key",
"id": "2e9ef09e-dfac-4526-96b4-d02f31af1b22",
"state": "active",
"size": 2048,
"algorithmRef": "crypto/algorithm/rsa-2048@1.2.840.113549.1.1.1",
"creationDate": "2016-11-21T08:00:00Z",
"activationDate": "2016-11-21T08:20:00Z"
},
"oid": "1.2.840.113549.1.1.1"
}
}
]
}Limitations of CBOM
Although CBOM provides a structured approach to cataloging cryptographic assets, it captures only static information — a snapshot of the current environment. Consequently, it is important to regularly refresh the inventory to account for changes.
Tools to Build a Cryptographic Inventory with CBOM
Several open-source tools are available to help organizations adopt CBOM. The table below covers scanning, storage, and analysis tools.
| Tool | Description |
|---|---|
| CBOM-Lens | CLI tool that scans filesystems, container images, and network ports for cryptographic assets and generates a CycloneDX CBOM 1.6. Supports scheduled scanning and PQC algorithm detection. Developed by OmniTrust. |
| CBOM-Repository | REST API service for storing, versioning, and searching CBOM documents. Built on S3-compatible backends with automatic version management and URN-based retrieval. Developed by OmniTrust. |
| CycloneDX CBOM | Overview of the CBOM standard with a list of available tools and the specification itself. |
| CBOMKit | Toolset designed to work with CBOM, offering features for cryptographic asset detection and management. |
| Sonar Cryptography Plugin | SonarQube plugin that detects cryptographic assets in source code and generates CBOMs. |
| CBOMkit-theia | Tool for detecting cryptographic assets in container images and directories, generating CBOMs. |
| Cryptobom Forge | Parses the output from CodeQL for cryptographic asset analysis and generates CBOMs. |
| CryptoMon | Analyzes over-the-wire TLS cryptography and generates CBOMs. |
Conclusion
Building a comprehensive cryptographic asset inventory is a vital step in migrating to post-quantum cryptography. As quantum computing continues to evolve, the need for organizations to protect their cryptographic infrastructure becomes more urgent. Ultimately, tools like CBOM provide a structured approach to managing cryptographic assets and preparing for the quantum future.
Specifically, by identifying, documenting, and assessing cryptographic assets now, businesses can significantly reduce their risk in the post-quantum era.