Most PKI environments grow organically and operate without structured governance — not from negligence, but because no framework existed to guide them. The PKI Maturity Model (PKIMM) changes that, providing a measurable way to identify gaps, prioritize improvements, and move from reactive operations to governed infrastructure.
The gap most PKI teams face is not tooling. It is governance. PKIMM gives that governance a structure.
You know the pattern. A certificate expires on a Friday night. Someone renews it manually, emails the team, and updates a spreadsheet — if the spreadsheet still exists. The CA that issued it runs a policy no one has reviewed since deployment. Three other CAs in the environment are undocumented.
This is not a tools problem. It is a governance problem. Moreover, regulatory pressure is making it urgent. NIS2, DORA, and eIDAS 2 all require proven control over cryptographic assets. Auditors no longer accept “we manage certificates” as sufficient. They want evidence of defined processes, measured compliance, and continuous improvement. An ad-hoc PKI cannot produce that evidence because the processes were never defined.
Without a maturity framework, improvement efforts tend to be reactive: fix the thing that failed last, buy the tool that addresses the loudest complaint. The result is patchwork — better in spots, still fragile overall.
The Ad-Hoc PKI Problem
In practice, PKI deployments rarely start with a governance plan. Instead, they start with a requirement: someone needs a certificate. A CA gets stood up. Then another. Certificates get created. Typically, tracking happens in spreadsheets, in someone’s memory, or not at all.
Over time, the environment accumulates familiar problems:
- Multiple CAs with overlapping or unclear trust boundaries.
- No centralized certificate inventory.
- Inconsistent key management practices across teams.
- Renewal processes that depend on calendar reminders and tribal knowledge.
- No documented policy for revocation decisions.
Ultimately, this is the natural result of PKI growing organically without a maturity framework to guide it. The infrastructure works — until it doesn’t. And when it fails, the blast radius is wide because no one has visibility into the full scope of what exists, who owns it, or what depends on it.
What the PKI Maturity Model Measures
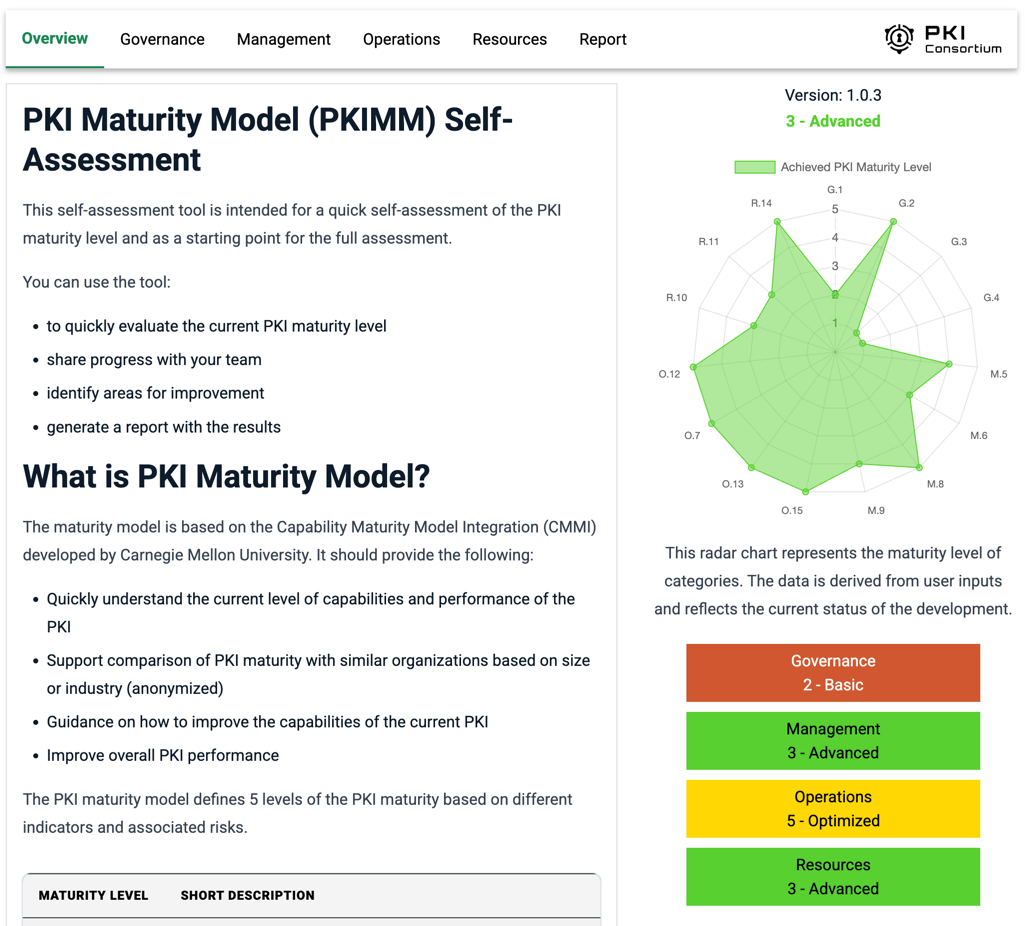
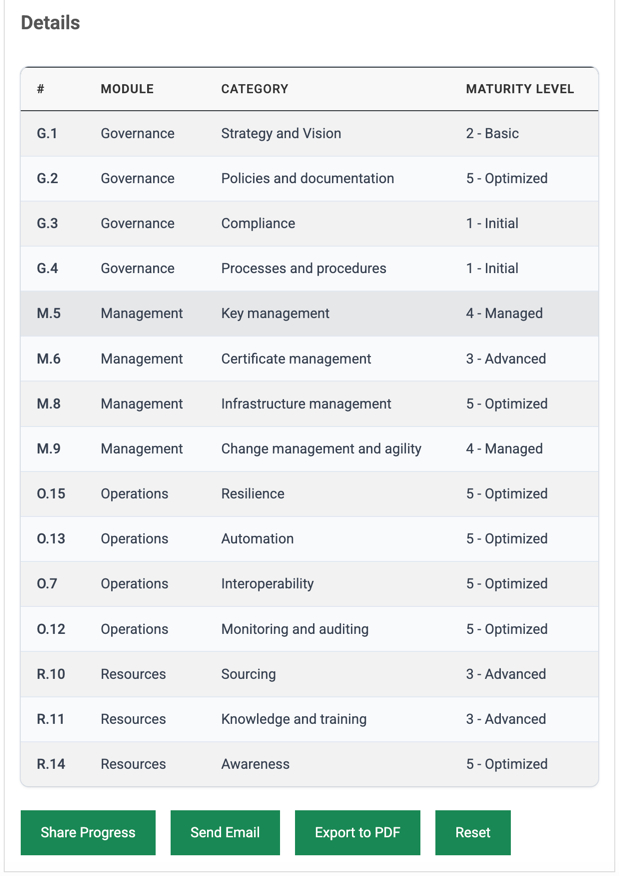
PKIMM, developed by the PKI Consortium’s PKIMM working group, provides a structured way to assess PKI operations. Instead of asking “is our PKI good enough?”, the model asks specific, measurable questions across defined categories. The online self-assessment tool lets you evaluate your organization in minutes and produces a radar chart showing maturity across all four modules.
The model defines five maturity levels:
- Initial — unpredictable processes with poor control; always reactive.
- Basic — processes exist per project or case, but controls are still mostly reactive.
- Advanced — processes follow organizational standards; controls are proactive.
- Managed — processes are measured and controlled with a proactive approach.
- Optimized — continuous improvement of processes, proactive approach for future technology.
Specifically, the model is based on CMMI and organizes 15 assessment categories into four modules: Governance (strategy and vision, policies and documentation, compliance, processes and procedures), Management (key management, certificate management, infrastructure management, change management and agility), Operations (resilience, automation, interoperability, monitoring and auditing), and Resources (sourcing, knowledge and training, awareness). Each category is scored on its own. Consequently, a team might score Managed in key management but Initial in compliance. Both scores matter, because that granularity is precisely the point — it reveals where to focus.
From Assessment to Roadmap
Running a PKIMM assessment is not an audit. Instead, it is a diagnostic. The output is a maturity profile: a map of where your organization stands across each category, with clear indicators of what the next level requires.
| Dimension | Ad-Hoc PKI | Governed PKI |
|---|---|---|
| Certificate discovery | Manual, incomplete | Automated, centralized inventory |
| Renewal process | Calendar reminders, tribal knowledge | Policy-driven, scheduled rotation |
| Key management | Per-team, inconsistent | Centralized, HSM-backed |
| Revocation decisions | Reactive, undocumented | Defined policy, documented criteria |
| Audit readiness | “We can explain if asked” | Continuous evidence trail |
Moving from the left column to the right does not happen through a single tool purchase. It happens through structured, step-by-step gains — exactly what PKIMM is designed to guide.
Specifically, the model converts vague priorities into executable projects. Instead of “improve our PKI,” you get a concrete target: “Our certificate management is at Basic. Reaching Advanced requires documented renewal procedures, automated discovery, and a defined revocation policy.” That specificity changes the conversation entirely.
PKIMM does not tell you what tools to buy. It tells you which operational gaps to close — and in what order.
The model also gives architects a shared language with executives. When a PKI architect tells a CISO “we need to improve our certificate management,” the typical response is “we already have a CA.” PKIMM reframes this conversation: “Our certificate management is at Basic. Advanced requires these specific capabilities. Here is the investment case.” As a result, maturity levels replace subjective claims with measurable positions.
From Assessment to Action
PKIMM identifies the gaps. Closing them is a different challenge — and there is no single tool that covers all 15 categories. Improving strategy and vision requires leadership alignment. Raising awareness and knowledge scores requires training programs. Better compliance requires documented controls and evidence trails. These are organizational changes, not product features.
However, several PKIMM categories — particularly certificate management, key management, and automation within the Management and Operations modules — do benefit from operational tooling. This is where platforms like ILM contribute. Specifically, ILM helps close gaps in certificate and key lifecycle operations: policy-driven issuance, automated rotation, centralized inventory, and audit trails. These capabilities map directly to the Management module categories that PKIMM assesses.
Importantly, tooling alone will not move an organization from Basic to Advanced across the board. The Governance module (strategy, policies, compliance, processes) and the Resources module (sourcing, knowledge, awareness) require investments that no platform can substitute. A realistic PKIMM improvement plan addresses all four modules, not just the ones that tooling can reach.
For organizations beginning their PKIMM journey, the practical path is straightforward:
- Run the PKIMM Self-Assessment to establish a baseline across all four modules.
- Identify the two or three categories with the widest gap between current and target maturity.
- Distinguish which gaps require organizational change (governance, training, policy) from those that require operational tooling (automation, lifecycle management, monitoring).
- Address both tracks in parallel — and re-assess on a regular cycle to measure progress.
Each cycle closes specific gaps rather than attempting to overhaul everything at once. That step-by-step, evidence-based approach is what makes PKIMM practical rather than aspirational. Teams that embed this cycle into their trust lifecycle management practice find that maturity improvements compound over time.
Key Takeaways
- Most PKI environments operate at ad-hoc maturity — not from negligence, but from organic growth without a governance framework.
- PKIMM provides a structured, measurable assessment across 15 categories in four modules and five maturity levels (Initial through Optimized).
- The model converts vague “improve PKI” priorities into specific, actionable improvement roadmaps with concrete targets.
- PKIMM creates a common language between architects and executives — maturity levels replace subjective claims with measurable positions.
- Tooling like ILM helps close gaps in the Management and Operations modules (certificate management, key management, automation), but Governance and Resources require organizational change that no platform can substitute.
Start with a baseline. Run the PKIMM Self-Assessment to see where your PKI operations stand today — then build the improvement roadmap from evidence, not intuition.